The Hardware Security Group focuses on the following research topics: side-channel analysis attacks, manipulation attacks, algorithmic, and holistic methods to reduce the success of physical attacks, methodology for developing designs that are resistant against a broad spectrum of physical attacks. The vision of the Hardware Security Group is that in future, designers (even without deep knowledge of different attacks) can develop circuits with high resistance to a broad spectrum of physical attacks using a "security optimization" option of an automated design tool. Design methodology for the engineering resistant circuits is an important step for engineering resilient systems.
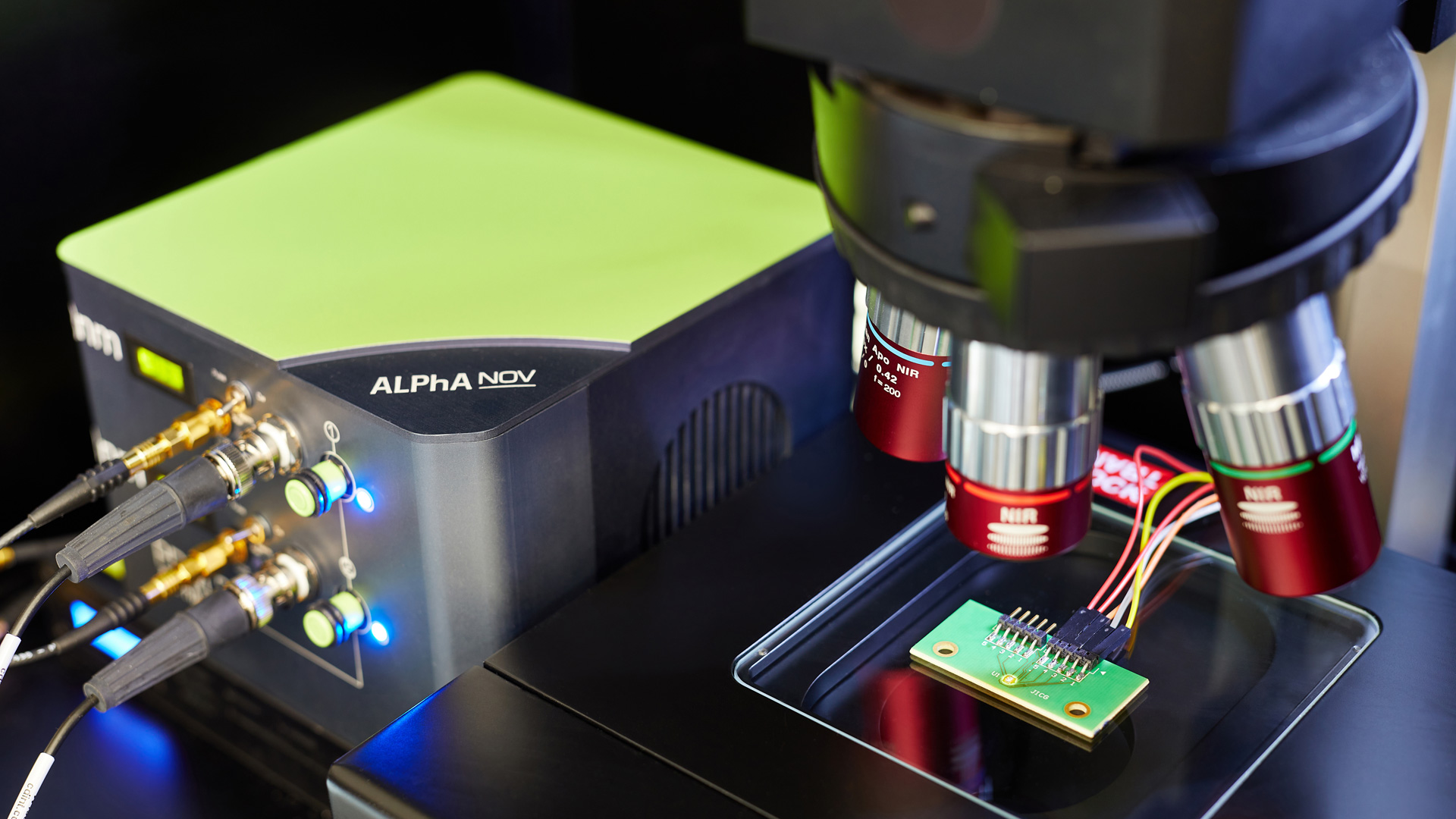
Cryptographic algorithms are nowadays the main means for implementing security requirements. There are many standardised cryptographic protocols for key exchange, encryption, and decryption of data, (mutual) authentication, generation, and verification of digital signatures. Cryptographic operations are based on complex mathematical operations and are therefore often implemented in hardware as specialised ASICs to reduce the execution time and energy consumption. The effectiveness of cryptographic methods is based on the secrecy of private keys. If attackers have physical access to the cryptographic chips, the cryptographic implementations can be attacked analysing so-called side-channel effects, i.e. the current through the cryptographic ASICs, their electromagnetic emissions, execution time, and many other physical effects. The side-channel effects can be measured by the attacker and statistically evaluated with the goal to reveal the cryptographic private key. Another type of attack is a manipulation of the behaviour of cryptographic ASICs using fault injections. The Hardware Security Group focuses not only on cryptographic circuits but also on the resistance investigation of RRAM cells. Methods increasing resistance are highly important when using RRAM structures as hardware accelerators for Artificial Intelligence (AI) methods. A starting point is the resistance of the IHP RRAMs against manipulation, e.g. against optical (laser) fault injections.
The first steps are collection, analysis, checking, and systematization of already known "partial solutions" reducing the success of physical attacks. Systematized holistic solutions, knowledge, and criteria are the basis of the design methodology for engineering circuits resistant to a broad spectrum of physical attacks.
Main target
- Development of a design methodology for engineering circuits that are resistant against a broad spectrum of physical attacks
Research topics
- Hardware security
- Side-channel attacks: analysis and countermeasures
- Efficient implementations of cryptographic algorithms in hardware
- Resistance of AI accelerators against physical attacks
- Application of AI methods for designing resistant circuits
Research results
- Vulnerability of IHP logic gates, JICG & TMR registers, and RRAM structures, to optical FI demonstrated
- Dependability of the design resistance on target frequency, technology node, cell libaries, etc. demonstrated
- Vulnerability of regularity & atomicity principles to simple SCA demonstrated, countermeasures proposed