The research of the Cyber-Physical System Engineering department addresses the challenges that arise from increasingly complex systems, e.g. through autonomously acting devices, increasing threats in the area of cyber security, and growing demands for privacy protection, e.g. in the area of personalized medical devices, etc.
The strategic goal of the department can be summarized in the following
“Enabling a trustworthy, reliable and intelligent cyber-physical world”
To achieve this goal, research is conducted at the highest international level in the following areas:
- Investigation and provision of a design methodology for resilient, trustworthy, reliable and intelligent cyber-physical systems
- Research into AI concepts that enable devices/machines to deal with unexpected situations
- Research into AI-based approaches for self-monitoring, self-optimization, self-healing and prediction of future system states
- Research into multi-input cognitive sensors (MICS) to improve, for example, situational awareness, self-monitoring, etc.
- Research and provision of core components for resilient systems, i.e. components for decision making, security, redundancy, self-healing, etc.
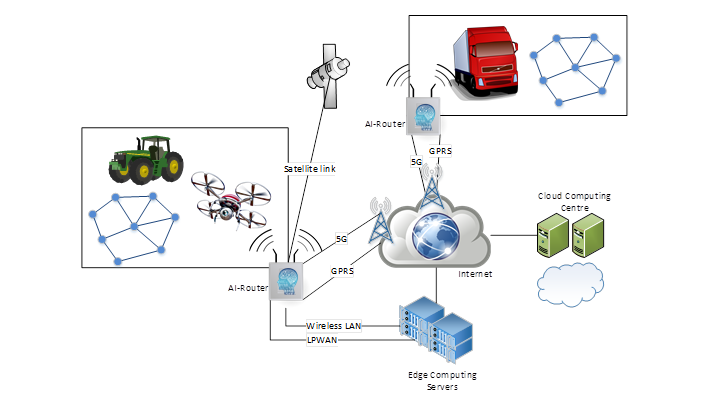
The three working groups of the department, Security & Resilience Engineering (SRE), Intelligent IoT Systems (IIoT) and Proactive Computing (PC), respectively address different phases in the life cycle of cyber-physical systems. SRE focuses on the design phase, i.e. in particular on how non-functional properties of a system can be integrated into it at an early stage and how their presence can be evaluated. IIoT focuses on the implementation phase, i.e. how the specification of a CPS can be implemented in a specific real environment so that the relevant properties are fully preserved. CP is dedicated to the runtime of the CPS and investigates how the important properties of the CPS can be ensured under changing conditions, including approaches for the early detection or even prediction of changes.